Security Code Review


Overview
What is Security Code Review?
Security Code Review is a detailed examination of an application’s source code to identify security vulnerabilities before deployment. Our expert security analysts review the code manually and through automated tools to detect issues like insecure authentication, improper error handling, SQL injection risks, and more.
This proactive approach strengthens your application’s security posture and ensures compliance with industry security standards.
Key Benefits
Why You Need a Security Code Review
Cyphire is a fully managed service that helps security teams quickly identify and remediate exposures before attackers can strike. Cyphire liberates the potential of your business with adaptable identity solutions forged in the world’s toughest markets.
we can do one section regarding "Our Methodology" in the security code review service:
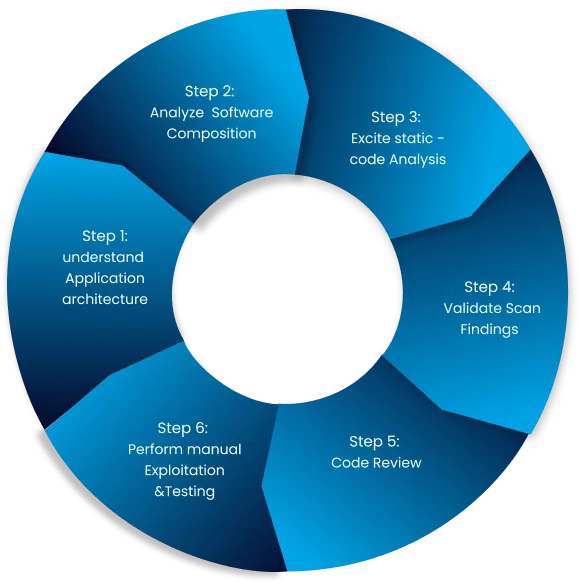
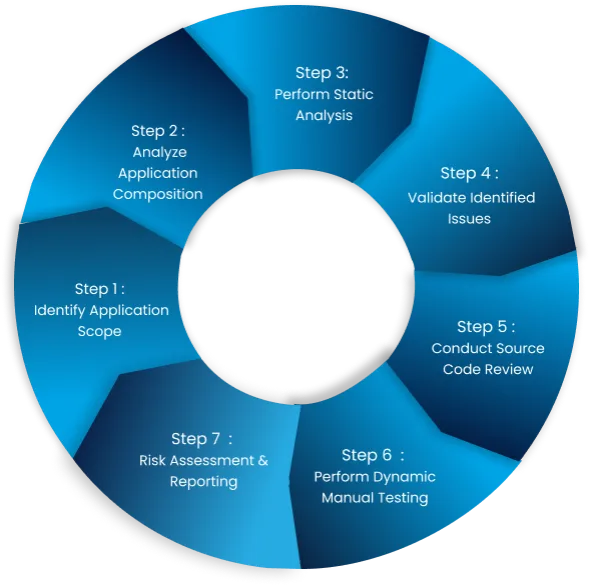
Understand Application Architecture
-Map the application’s components and their interactions.
-Identify key modules, frameworks, and external dependencies.
Analyze Software Composition
-Identify third-party libraries and frameworks.
-Review dependency trees and check for known vulnerabilities (using tools like OWASP Dependency-Check).
Automated Static Code Analysis
-Perform automated scans using tools like SonarQube, , or Semgrep.
-Focus on identifying common vulnerabilities, such as injection flaws, XSS, and insecure configurations.
Validate Findings
-Manually inspect the flagged issues to eliminate false positives.
-Map findings to OWASP Top 10 or ASVS for prioritization.
Manual Code Review
-Review critical areas of the code, including:
-Input validation and output encoding.
-Authentication and authorization logic.
-Cryptographic implementations.
-Error handling and logging.
-Cross-reference with security requirements and business logic.
Report Findings and Recommendations
-Document findings with clear remediation guidance.
-Prioritize issues by severity and risk.

Early Detection of Vulnerabilities
Identify vulnerabilities before hackers do and secure your mobile app against potential threats.

Cost-Effective Security Measure
Fixing vulnerabilities in the development phase is significantly cheaper than post-deployment fixes.

Compliance with Security Standards
Ensure adherence to security frameworks such as OWASP, PCI-DSS, and GDPR.

Enhanced User Trust
Show your customers you care about their security, building lasting loyalty and increasing conversions.

Business Continuity
Minimize downtime and prevent costly interruptions to your operations caused by cyberattacks.

Actionable Security Insights
Get detailed, actionable reports that prioritize fixes, helping you strengthen your defenses and meet critical deadlines.
Numbers That Speak Security
Securing the Future, One Vulnerability at a Time

Years of cybersecurity expertise
Applications Secured
Clients protected
Put Your Cloud to the Ultimate Test
Why Choose Us?
With a team of certified ethical hackers and cybersecurity experts, we bring years of experience in securing mobile applications across various industries. Our penetration testing approach goes beyond automated scans—we perform thorough manual testing to identify complex security flaws. We provide clear, detailed reports with remediation guidance, helping your development team address vulnerabilities effectively. Partner with us for reliable, efficient, and industry-compliant security testing services that protect your mobile application from ever-evolving cyber threats.
Ask Question
Revolutionizing For Technology Future
What is the difference between security code review and penetration testing?
When should I conduct a security code review?
Does a security code review impact application performance?
How long does a security code review take?
Will I receive recommendations for fixing identified issues?


