Mobile Application
Penetration Testing


Overview
What is Mobile Application Penetration Testing?
Mobile Application Penetration Testing is a security assessment designed to simulate real-world cyberattacks on mobile applications. This process uncovers vulnerabilities and weaknesses that could be exploited by malicious actors.
Our methodology adheres to industry-leading frameworks, including the OWASP Mobile Security Testing Guide (MSTG), ensuring a thorough and reliable evaluation. By simulating attack scenarios, we identify critical risks such as insecure data storage, API vulnerabilities, authentication flaws, and code-level security issues.

Key Benefits
Why You Need Mobile Application Penetration Testing
Cyphire is a fully managed service that helps security teams quickly identify and remediate exposures before attackers can strike. Cyphire liberates the potential of your business with adaptable identity solutions forged in the world’s toughest markets.
we can do one section regarding "Our Methodology" in the mobile app service:
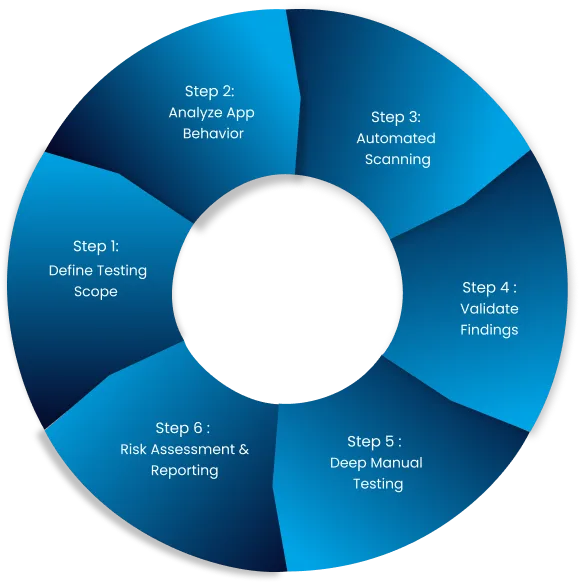
Define Testing Scope
-Understand app functionality, architecture, and key components (client-side, server-side, APIs).
Analyze App Behavior
– Perform static analysis through code review or reverse engineering.
Automated Scanning
– Use tools to detect common vulnerabilities like insecure communication and storage.
Validate Findings
– Confirm and eliminate false positives from automated scans.
Manual Testing
– Conduct runtime analysis, reverse engineering, API testing, and exploit vulnerabilities.
Risk Assessment & Reporting
– Assess vulnerabilities, prioritize based on risk, and provide actionable recommendations.

Protect Sensitive User Data
Avoid data breaches by identifying vulnerabilities that could expose customer information, protecting your app and brand reputation.

Prevent Costly Security Breaches
Address vulnerabilities before attackers exploit them, saving your business from potential financial and reputational losses.

Ensure Compliance with Standards
Meet security requirements like OWASP MSTG, HIPAA, SOC2 and PCI-DSS to stay compliant and avoid penalties.

Strengthen Customer Trust
Demonstrate your commitment to security, giving users confidence in your mobile app and business.

Stay Ahead of Evolving Threats
Simulate real-world attack scenarios to uncover weaknesses before hackers do, keeping your app resilient as threats evolve.

Optimize Development Practices
Empower your development team with clear, actionable insights to build more secure apps and prevent recurring vulnerabilities.
Numbers That Speak Security
Securing the Future, One Vulnerability at a Time

Years of cybersecurity expertise
Applications Secured
Clients protected
Put Your Mobile App to the Ultimate Test
Why Choose Us?
Our team of certified ethical hackers and cybersecurity experts has extensive experience securing mobile applications across diverse industries. We combine advanced manual testing techniques with industry-leading methodologies to uncover complex vulnerabilities that automated scans cannot detect.
Our team of certified ethical hackers and cybersecurity experts has extensive experience securing mobile applications across diverse industries. We combine advanced manual testing techniques with industry-leading methodologies to uncover complex vulnerabilities that automated scans cannot detect.
We deliver clear and detailed reports, providing actionable remediation guidance to help your development team address vulnerabilities efficiently. Our services are reliable, efficient, and designed to meet industry compliance standards, ensuring your mobile application is protected against evolving cyber threats. Partner with us to safeguard your app, enhance resilience, and build trust with your users.
Ask Question
Secure Your Mobile Application
What is the difference between mobile and web penetration testing?
How often should I conduct a penetration test for my mobile app?
Will penetration testing disrupt my mobile application's functionality?
What kind of report will I receive after the penetration test?
Can penetration testing help with compliance requirements?


