Strengthen Your Network Security Against External and Internal Threats


Overview
What is External & Internal Network Penetration Testing?
Key Benefits
Why You Need External & Internal Network Penetration Testing
Cyphire is a fully managed service that helps security teams quickly identify and remediate exposures before attackers can strike. Cyphire liberates the potential of your business with adaptable identity solutions forged in the world’s toughest markets.

we can do one section regarding "Our Methodology" in theExternal & Internal Network Penetration Testing service:
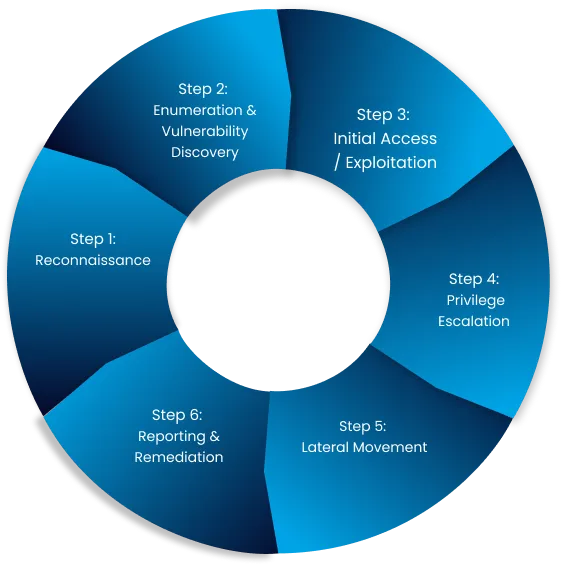
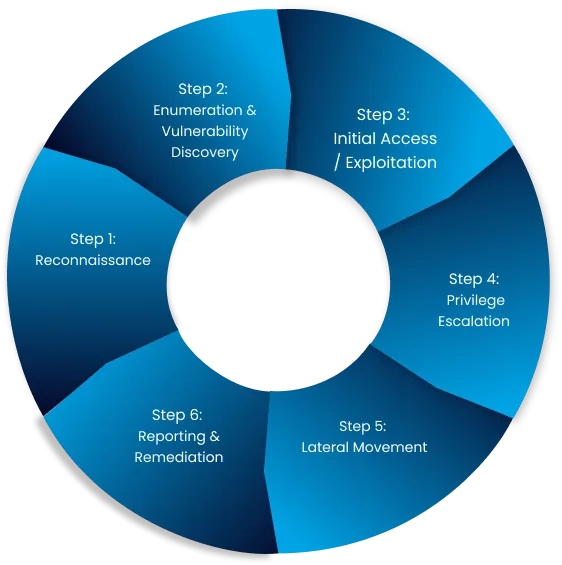
Reconnaissance
– Gather public and internal data about the network.
– MITRE Tactics: *Reconnaissance*
– Techniques: Active scanning, OSINT tools (e.g., Shodan, Maltego).
Enumeration & Vulnerability Discovery
– Identify open ports, services, and vulnerabilities.
– MITRE Tactics: *Discovery*
– Tools: Nmap, Nessus, or custom scripts.
Initial Access / Exploitation
– Exploit discovered vulnerabilities to gain entry.
– MITRE Tactics: *Initial Access*
– Techniques: Phishing, unpatched exploits, weak credentials.
Privilege Escalation
– Elevate access from user to administrative level.
– MITRE Tactics: *Privilege Escalation*
– Techniques: Credential dumping, exploiting misconfigurations.
Lateral Movement
– Access additional systems in the network.
– MITRE Tactics: *Lateral Movement*
– Techniques: Pass-the-Hash, exploiting RDP or SMB shares.
Reporting & Remediation
– Document findings with MITRE ATT&CK mappings.
– Provide prioritized, actionable remediation steps.

Early Detection of Vulnerabilities
dentify and address vulnerabilities before hackers strike, protecting your business from costly breaches and downtime.

Cost-Effective Security Measure
Avoid hefty fines and legal risks by ensuring your app meets GDPR, HIPAA, and PCI-DSS compliance with ease.

Compliance with Security Standards
Protect your customers’ trust and your business reputation by preventing unauthorized access to critical data.

Improved Code Quality
Show your customers you care about their security, building lasting loyalty and increasing conversions.

Protection Against Common Attacks
Minimize downtime and prevent costly interruptions to your operations caused by cyberattacks.

Actionable Insights for Developers
Get detailed, actionable reports that prioritize fixes, helping you strengthen your defenses and meet critical deadlines.
Numbers That Speak Security
Securing the Future, One Vulnerability at a Time

Years of cybersecurity expertise
Applications Secured
Clients protected
Put Your Cloud to the Ultimate Test
Why Choose Us?
Our security experts specialize in conducting thorough penetration testing across both external and internal network environments. We combine automated scanning with advanced manual testing techniques to uncover security flaws that could be exploited by cybercriminals. Our reports provide clear, detailed findings and step-by-step remediation guidance, helping your IT team enhance network security efficiently. With a commitment to compliance, security, and risk mitigation, we ensure your network remains resilient against evolving threats.
Ask Question
Revolutionizing For Technology Future
What is the difference between external and internal penetration testing?
External testing evaluates public-facing network components, while internal testing assesses risks within your internal infrastructure.
Will network penetration testing disrupt business operations?
How often should I conduct network penetration testing?
What types of vulnerabilities do you look for?
Will I receive a remediation report after the test?


