Web Application Penetration Testing
Cyphire combines the top minds in offensive security with advanced weaponry and tactics to help organizations across the globe proactively assess the security of their products, applications, networks, and cloud infrastructure.

Overview
What is Web Application
Penetration Testing?
Web Application Penetration Testing is a simulated cyberattack designed to uncover vulnerabilities in your web application. Using industry-standard frameworks like OWASP, we identify critical risks such as SQL injection, cross-site scripting (XSS), and authentication flaws.
Our testing not only strengthens your application’s security but also helps you meet compliance requirements, including SOC 2, PCI-DSS, and HIPAA. With actionable insights from real-world attack simulations, you can protect sensitive data, maintain user trust, and safeguard your business operations.



Key Benefits
Why You Need Web Application Penetration Testing
Your web applications are the backbone of your business—and the #1 target for cybercriminals. Without proactive testing, your business faces serious risks:
- Data Breaches: Sensitive customer and company data could be exposed, damaging your reputation and trust.
- Compliance Failures: Non-compliance with SOC 2, GDPR, or PCI-DSS could lead to fines and legal repercussions.
- Downtime Costs: A single vulnerability could disrupt operations and cost you thousands—or millions.
At Cyphire, we simulate real-world cyberattacks to identify vulnerabilities before attackers can exploit them. From SQL injection and XSS to broken access controls, our Web Application Penetration Testing ensures your applications are secure, resilient, and compliant.
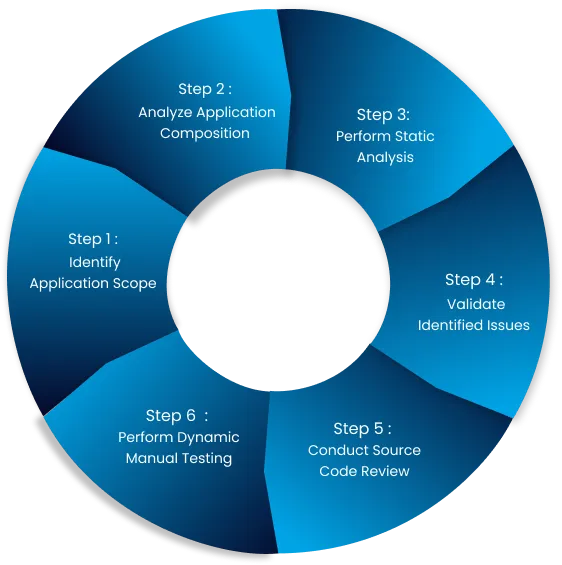
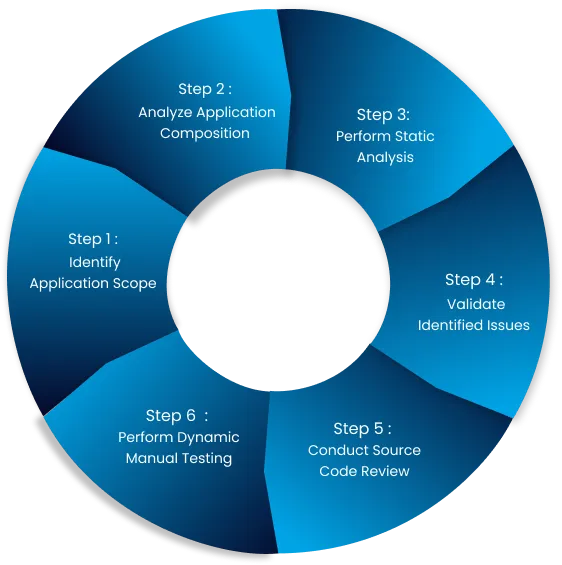
we can do one section regarding "Our Methodology" in the web app service:
Analyze/Crawl Application
Understand the application's architecture, data flows, and functionality through static and dynamic crawling.
Identify Attack Surface
Map all endpoints, user inputs, APIs, and components to pinpoint areas vulnerable to attack.
Automated Scanning
Use tools to detect common vulnerabilities like XSS, SQL injection, and security misconfigurations.
Validate Findings
Manually verify vulnerabilities detected in automated scans to confirm their accuracy and potential impact.
Deep Manual Testing
Conduct advanced tests on authentication, session management, access controls, and injection points. Exploit vulnerabilities where possible.
Reporting
Document findings with clear risk assessments and remediation recommendations tailored to the application.

Proactive Security Assessment
dentify and address vulnerabilities before hackers strike, protecting your business from costly breaches and downtime.

Compliance and Regulatory Adherence
dentify and address vulnerabilities before hackers strike, protecting your business from costly breaches and downtime.

Protection Against Data Breaches
dentify and address vulnerabilities before hackers strike, protecting your business from costly breaches and downtime.

Enhanced User Trust
dentify and address vulnerabilities before hackers strike, protecting your business from costly breaches and downtime.

Business Continuity
Minimize downtime and prevent costly interruptions to your operations caused by cyberattacks.

Actionable Security Insights
Get detailed, actionable reports that prioritize fixes, helping you strengthen your defenses and meet critical deadlines.
Numbers That Speak Security
Securing the Future, One Vulnerability at a Time

Years of cybersecurity expertise
Applications Secured
Clients protected
Put Your Web Application to the Ultimate Test
Why Choose Us?
With a team of certified ethical hackers and cybersecurity experts, we bring decades of experience to every engagement. Our Web Application Penetration Testing goes beyond automated tools—we employ advanced manual techniques to uncover even the most elusive vulnerabilities.
What We Deliver
- Comprehensive Reports: Actionable insights with step-by-step remediation guidance.
- Tailored Testing: Custom strategies designed to address your specific goals—whether you need to meet compliance standards like SOC 2, GDPR, or PCI-DSS, or enhance your overall security posture.
- Customer-Centric Focus: We take the time to understand your unique business needs and deliver solutions aligned with your priorities, ensuring meaningful results.
- Proven Expertise: Trusted by global enterprises and government contractors for over 15 years.
Ask Question
Frequently Asked Questions (FAQ)
What is the difference between automated and manual penetration testing?
Why is penetration testing important for my web application?
How often should I perform a penetration test?
Will penetration testing disrupt my application?
What types of vulnerabilities does penetration testing uncover?
What kind of report will I receive after the penetration test?
Can penetration testing help with compliance requirements?
What are black-box, gray-box, and white-box penetration tests?


